
内存取证检测恶意木马
27页1、Detecting Malware With Memory Forensics Hal Pomeranz SANS Institute Why Memory Forensics? Everything in the OS traverses RAM Processes and threads Malware (including rootkit technologies) Network sockets, URLs, IP addresses Open files User generated content Passwords, caches, clipboards Encryption keys Hardware and software configuration Windows registry keys and event logs Memory Analysis Advantages Best place to identify malicious software activity Study running system configuration Identify i
2、nconsistencies (contradictions) in system Bypass packers, binary obfuscators, rootkits (including kernel mode) and other hiding tools. Analyze and track recent activity on the system Identify all recent activity in context Profile user or attacker activities Collect evidence that cannot be found anywhere else Memory-only malware Chat threads Internet activities What is Memory Forensics? Study of data captured from memory of a target system Ideal analysis includes physical memory data (from RAM)
3、as well as Page File (or SWAP space) data Acquire Capture Raw Memory Hibernation File Context Establish Context Find Key Memory Offsets Analyze Analyze Data For Significant Elements Recover Evidence Windows Memory Acquisition LIVE System (RAM Acquisition) DumpIt.exe http:/ win32dd.exe / win64dd.exe Author: Matthew Suiche http:/ Mandiant Redline http:/ DEAD System Hibernation File Contains a compressed RAM Image %SystemDrive%/hiberfil.sys Win2k XP Win2003 VISTA Win2008 Windows 7 Virtual Machine M
4、emory Acquisition VMware (Fusion/Workstation/Server/Player) .vmem file = raw memory image Microsoft Hyper-V .bin file = raw memory image Parallels .mem file = raw memory image VirtualBox .sav file = partial memory image Extract Memory from Hibernation File (hiberfil.sys) hibr2bin can acquire physical memory (RAM) from a Windows hibernation file (XP and VISTA only) Pro Version Compatible with XP-Win7/2008 (32 and 64 bit) hibr2bin.exe Location on COURSE DVD: D:windows forensic toolsmemory imaging
《内存取证检测恶意木马》由会员第***分享,可在线阅读,更多相关《内存取证检测恶意木马》请在金锄头文库上搜索。
校园足球汇报
异甘草酸镁注射液【治疗急性药物性肝损伤】Ⅱ期临床研究总结
云教室课程行政伦理学行政良心

语文S版小学二年级语文下册诺亚方舟课件优质课教学课件
未来中考趋势作文考与练
近年来广东历史试题中考易错点分析与教学启示

搜索推广那些事

小学语文二年级上册红领巾真好说课稿设计(说课设计)

新课标人教版二年级语文上册红领巾真好课件

新课程背景下的高中化学课堂教学改革

危机管理与突发事件应对

背影朱自清教案课件二课时
突发公共卫生事件培训
统计学简史及数据科学中南财经大学

水泥混凝土路面技术现状及发展终
有家真好作文讲评课
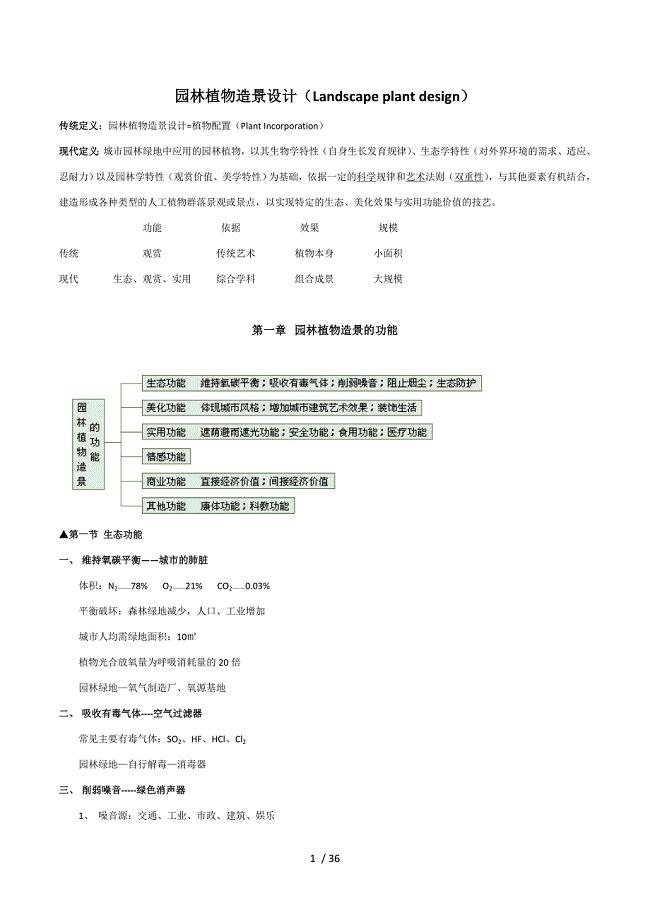
西南大学植物造景设计总复习
海外汉语教学新探索在线交流学习平台Goclef

动态黑色背景年终总结模板
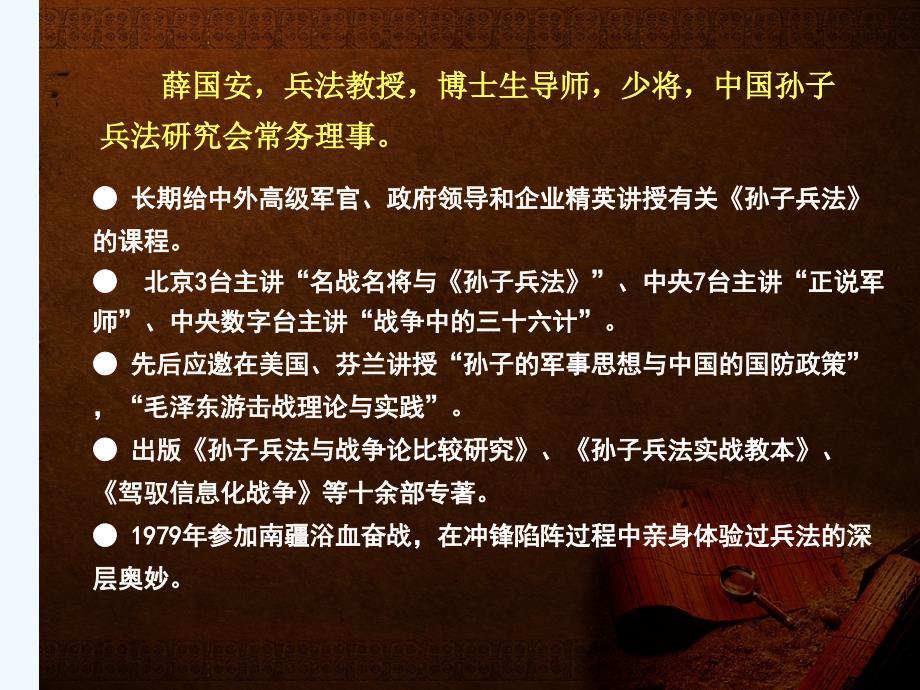
孙子的治军之道与现代管理谋略总结
 公司治理迪斯尼童话般的公司治理
公司治理迪斯尼童话般的公司治理
2022-09-30 8页
 电动单梁起重机安全系统管理系统规章制度总汇编
电动单梁起重机安全系统管理系统规章制度总汇编
2022-11-29 26页
 年产3000吨精密有色金属铸件技术改造项目可行性研究报告
年产3000吨精密有色金属铸件技术改造项目可行性研究报告
2023-10-07 82页
 AMBAAHBAPBBUS
AMBAAHBAPBBUS
2022-11-09 3页
 4月浙江省普通高校招生选考科目考试物理选考试卷版含答案
4月浙江省普通高校招生选考科目考试物理选考试卷版含答案
2023-02-18 10页
 梵谷口腔医疗管理软件使用手册v3
梵谷口腔医疗管理软件使用手册v3
2023-10-13 56页
 计算机软件基础
计算机软件基础
2023-07-06 6页
 仓库搬迁工作计划怎么写附模板
仓库搬迁工作计划怎么写附模板
2023-02-01 3页
 年产24万吨饲料建设项目可行性研究报告
年产24万吨饲料建设项目可行性研究报告
2023-01-24 70页
 川大16计算机应用基础第一次作业答案
川大16计算机应用基础第一次作业答案
2023-10-18 7页

